Quick-Start 截图软件 Guide: Mastering Efficiency in Minutes
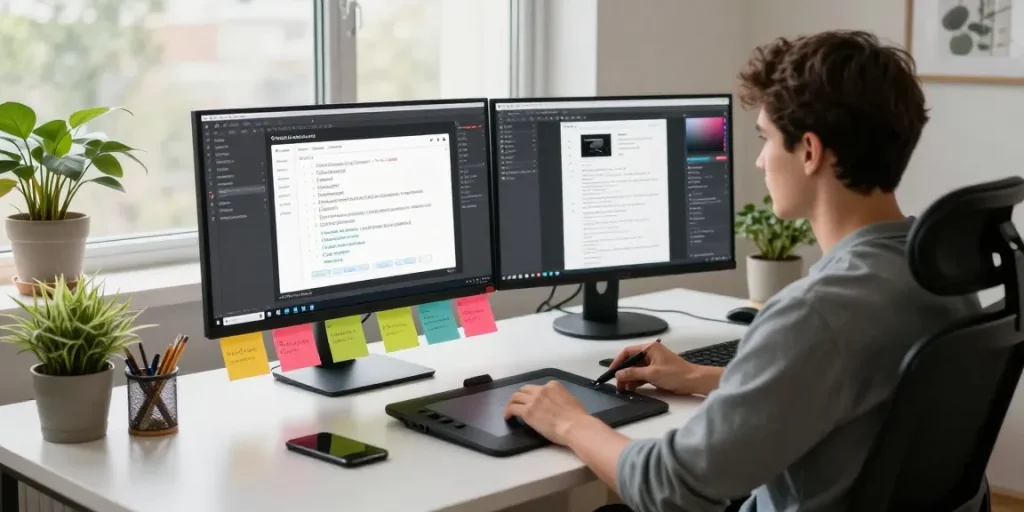
Understanding 截图软件: An Overview In an era where digital communication forms the backbone of productivity, efficient tools for capturing and sharing information are crucial. 截图软件, or screenshot software, plays a pivotal role in facilitating this process. From developers documenting coding sessions to educators presenting material, the applications of screenshot software are broad and varied. These…
Read more